CYCLONE-User-Manual.pdf - 第57页
User Manual For Cyclone LC Programmers 57 6.1.8.1.1 Creating an ImageKey If an ImageKey has not been created or a new ImageKey is required, the user should select the “Image Encryption” combo-box in the Cyclone Image Cre…

User Manual For Cyclone LC Programmers 56
6.1.4.13 Program Serial Number
This command becomes available once a programming algorithm is selected. It will instruct the
Cyclone to program the serial number to the target once executed. As with other commands, the
serial number will not be programmed until the SAP operations are carried out.
Note:
6.1.5 Communication Mode and Rate Settings
Cyclone LC programmers support multiple communication modes and communication rates. A
user needs to select proper communication mode and rate from the drop down list after
programming operations are specified. The debug connector pin definitions are listed for
reference.
6.1.6 Target Voltage and Power Settings
A user may elect to use Cyclone to supply power to the target. In this case, the Target Voltage
specifies the target MCU I/O voltage level.
The user needs to take into account the power discharge time for the Power Down delay. The
reset driver delays, power stabilization time, and the target clock stabilization time should be
considered for the Power Up delay.
A checkbox is available for a user to instruct the Cyclone to turn off target power after SAP
operations. If unchecked, the target power will remain on.
The user has the option to provide Reset Delay if certain reset monitoring devices are used. The
Cyclone will delay for the specified time after allowing the target out of reset.
6.1.7 Image Description
The Cyclone Image Creation Utility allows the user to summarize the purpose of their current
configuration for future reference by adding text to the Image Description box. The description will
be either programmed into the Cyclone or saved into an encrypted file.
The image description will appear on the Cyclone’s touchscreen LCD for image identification. This
field will not affect the Cyclone’s operations with the target.
Tip: If your image will be encrypted, it can be helpful to indicate this as part of the Image
Description.
Figure 6-16: Image Description Box
6.1.8 ProCryption Security License Features
Cyclone FX programmers, and Cyclone LC programmers with the ProCryption Security
Activation License installed, can take advantage of the powerful security features that can be
configured in this area of the Cyclone Image Creation Utility.
6.1.8.1 SAP Image Encryption
Users can create unique ImageKeys which can be used to encrypt their programming images.
SAP images encrypted in this way can only be loaded onto a Cyclone that has been provisioned
with the identical ImageKey.
Note: Both the Cyclone and the ImageKey are needed to decrypt the image. If the ImageKey is later
removed from the Cyclone, the encrypted SAP image cannot be decrypted for programming.
Likewise, the encrypted image cannot be read on a PC.
This section will detail how to use the Cyclone Image Creation Utility to encrypt a SAP image. For
a more in-depth description of Cyclone SAP image encryption, please see CHAPTER 11 - SAP
IMAGE ENCRYPTION. For detailed information about how to use and manage encrypted
programming images during the production process, the user should refer specifically to Section
11.4 - Managing Encryption For Production Programming.
User Manual For Cyclone LC Programmers 57
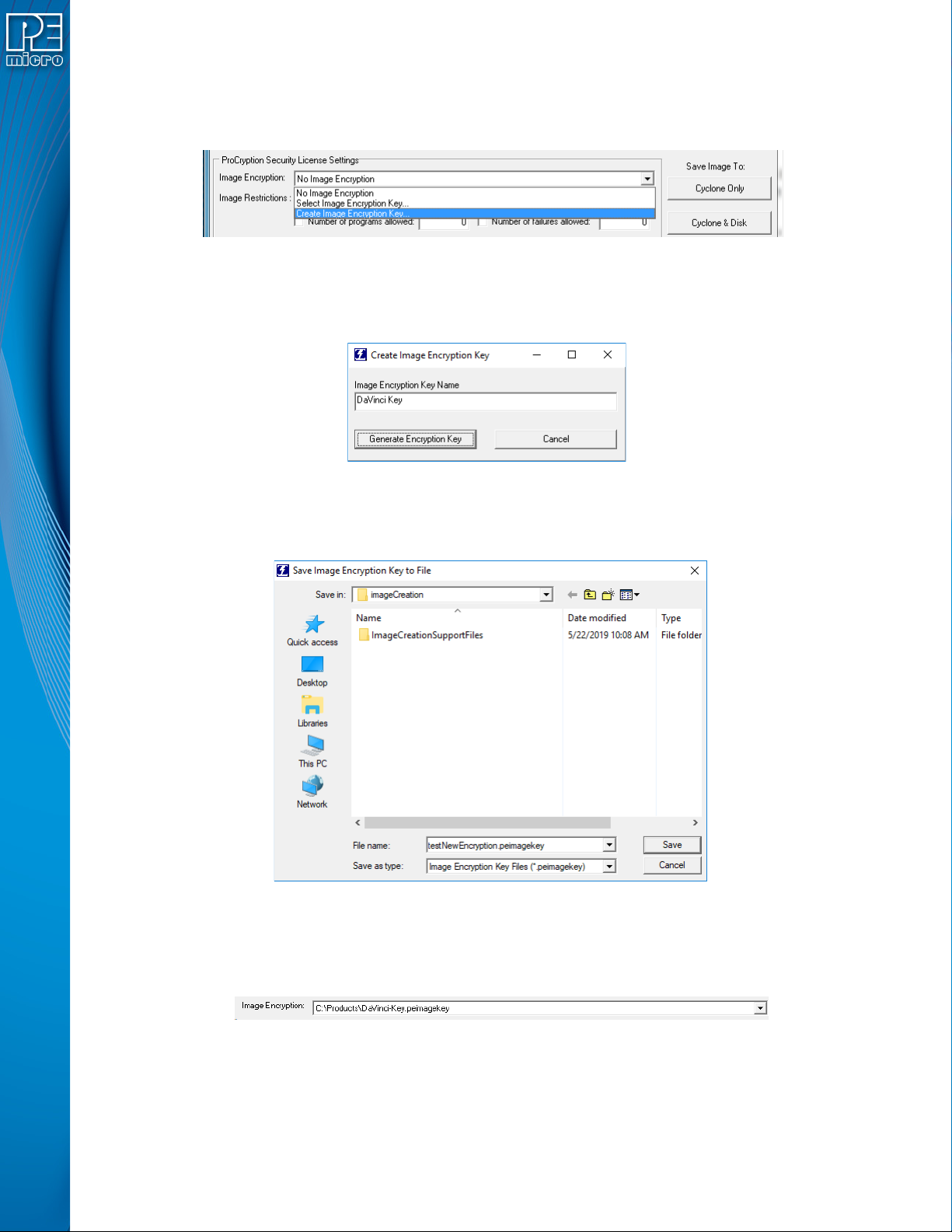
6.1.8.1.1 Creating an ImageKey
If an ImageKey has not been created or a new ImageKey is required, the user should select the
“Image Encryption” combo-box in the Cyclone Image Creation Utility and choose the “Create
Image Encryption Key...” option.
Figure 6-17: Create Image Encryption Key - Drop Box
This will pop up a box asking for a descriptive ImageKey Name (this name will be used for display
in many dialogs):
Figure 6-18: Create ImageKey
After entering the name, the user should click Generate Encryption Key. This will bring up a dialog
which allows the user to choose the save location:
Figure 6-19: Save Image Encryption Key To File Dialog
The user should navigate to the desired location and then click "Save". The ImageKey will be
generated and automatically selected in the Cyclone Image Creation Utility, such that generating
an image will use this ImageKey for encrypting.
Figure 6-20: ImageKey Selected After Creation
Note: Every ImageKey created is unique and may not be recreated. This means that once generated,
the user should keep the ImageKey in a secure place. Users may also wish to keep track of which
SAP images have been encrypted with each ImageKey, as the current software does not track this
information.
User Manual For Cyclone LC Programmers 58
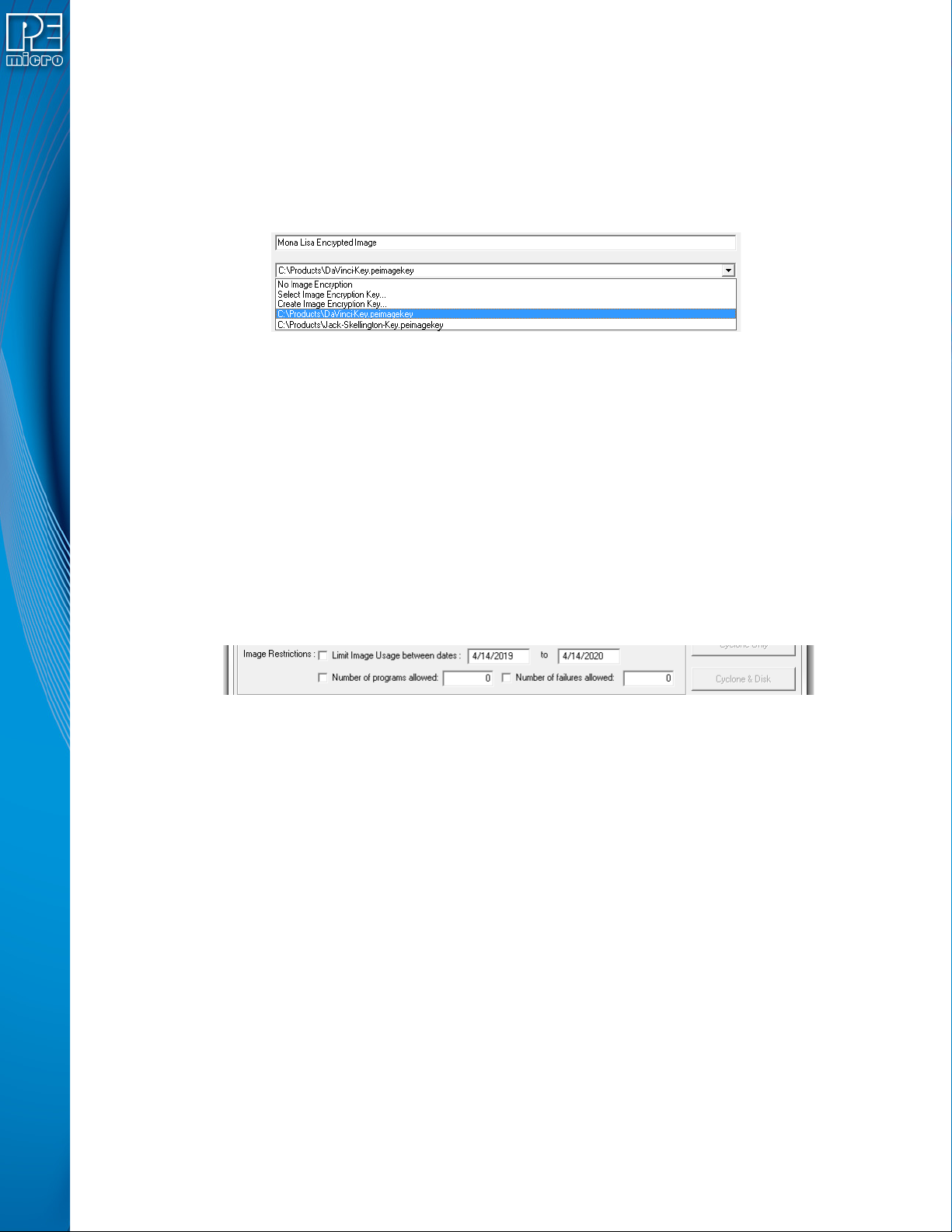
By default, the ImageKey will stay selected in the Image Creation Utility. If a different ImageKey is
required for encryption, or the user does not wish to encrypt their SAP image, the corresponding
change may easily be selected using the drop-down box.
6.1.8.1.2 Encrypting A SAP Image
To create an encrypted programming image, the user sets up their parameters in the Cyclone
Image Creation Utility as usual, and then simply selects the desired ImageKey in the "Image
Encryption" combo-box.
Figure 6-21: ImageKey Selection
The image will automatically be generated as an encrypted image, encrypted with the selected
ImageKey. An encrypted stand-alone programming image is called an eSAP (Encrypted Stand
Alone Programming) file. This eSAP file may be downloaded to any Cyclone which has been
provisioned with the same ImageKey (i.e. the ImageKey has already been added to the Cyclone).
This is discussed in Section 11.4.1 - Provisioning a Cyclone with an ImageKey.
6.1.8.2 Image Restrictions
There are any number of reasons why the user may want to place restrictions on the use of
specific programming images on a Cyclone programmer: from added ease when managing
production to a desire to protect intellectual property.
Cyclone FX programmers and Cyclone LC programmers with the ProCryption Security Activation
License are able to restrict the use of programming images via the associated fields in the Cyclone
Image Creation Utility.
Figure 6-22: Image Restrictions
This area allows you to specify one or more restrictions and tie them to specific programming
images. Even if restricted programming images are deleted from Cyclone’s internal memory or an
SD card, the Cyclone platform has a persistent memory that continues to tie security restrictions to
that programming image. Thus, if an image is removed and re-added to a Cyclone, the image
counts are maintained and would continue counting from where it left off. Also, if the SD Card is
moved from Cyclone to Cyclone, the count is maintained in both Cyclones as well as the SD Card.
Every time an image is generated by the Cyclone Image Creation utility, it is encoded with a unique
image ID number. All counts are stored relative to this unique ID number. So, when an image is
regenerated in the Cyclone Image Creation utility, it will have its own counts which will not conflict
with the previously generated image, even if the images are otherwise exactly the same. In this
way, the user can regenerate an image to allow a new batch of targets to be programmed.
Note: The user may set more than one type of restriction on a programming image. The ability to
program the image will be restricted by whichever triggers first. E.g., if the user creates settings to
allow 100 programs, and also sets an allowed date range restriction, the ability to program the
image will be restricted as soon as the first of these conditions is triggered.
Currently the user may set the following restrictions:
6.1.8.2.1 Limit Image Usage Between Dates
When “Limit Usage Between Dates” is checked and the start and end dates are specified with valid
dates (format: DD/MM/YYYY), the Cyclone operator will only be allowed to program the